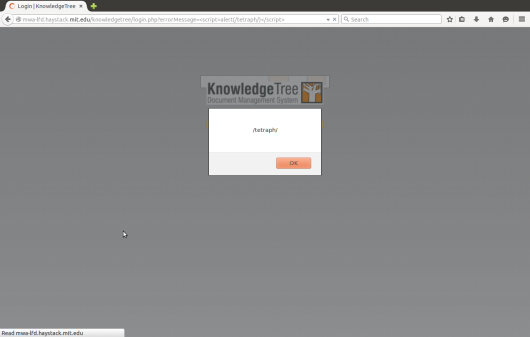
KnowledgeTree OSS 3.0.3b Reflected XSS (Cross-site Scripting) Web Application 0-Day Security Bug
Exploit Title: KnowledgeTree login.php &errorMessage parameter Reflected XSS Web Security Vulnerability
Product: Knowledge Tree Document Management System
Vendor: Knowledge Inc
Vulnerable Versions: OSS 3.0.3b
Tested Version: OSS 3.0.3b
Advisory Publication: August 22, 2015
Latest Update: August 31, 2015
Vulnerability Type: Cross-Site Scripting [CWE-79]
CVE Reference:
Impact CVSS Severity (version 2.0):
CVSS v2 Base Score: 4.3 (MEDIUM) (AV:N/AC:M/Au:N/C:N/I:P/A:N) (legend)
Impact Subscore: 2.9
Exploitability Subscore: 8.6
CVSS Version 2 Metrics:
Access Vector: Network exploitable; Victim must voluntarily interact with attack mechanism
Access Complexity: Medium
Authentication: Not required to exploit
Impact Type: Allows unauthorized modification
Discover and Reporter: Wang Jing [School of Physical and Mathematical Sciences (SPMS), Nanyang Technological University (NTU), Singapore] (@justqdjing)
Caution Details:
(1) Vendor & Product Description:
Vendor:
KnowledgeTree
Product & Vulnerable Versions:
Knowledge Tree Document Management System
OSS 3.0.3b
Vendor URL & Download:
Product can be obtained from here,
http://download.cnet.com/KnowledgeTree-Document-Management-System/3000-10743_4-10632972.html
http://www.knowledgetree.com/
Product Introduction Overview:
“KnowledgeTree is open source document management software designed for business people to use and install. Seamlessly connect people, ideas, and processes to satisfy all your collaboration, compliance, and business process requirements. KnowledgeTree works with Microsoft® Office®, Microsoft® Windows® and Linux®.”
(2) Vulnerability Details:
KnowledgeTree web application has a computer security problem. Hackers can exploit it by reflected XSS cyber attacks. This may allow a remote attacker to create a specially crafted request that would execute arbitrary script code in a user’s browser session within the trust relationship between their browser and the server.
Several other similar products 0-day vulnerabilities have been found by some other bug hunter researchers before. KnowledgeTree has patched some of them. “Bugtraq is an electronic mailing list dedicated to issues about computer security. On-topic issues are new discussions about vulnerabilities, vendor security-related announcements, methods of exploitation, and how to fix them. It is a high-volume mailing list, and almost all new vulnerabilities are discussed there.”. It has listed similar exploits, such as Bugtraq (Security Focus) 32920.
(2.1) The code flaw occurs at “&errorMessage” parameter in “login.php” page.
One similar bug is CVE-2008-5858. Its X-Force ID is 47529.
References:
http://seclists.org/oss-sec/2015/q3/458
http://tetraph.com/security/xss-vulnerability/knowledgetree-oss-3-0-3b-reflected-xss/
https://progressive-comp.com/?l=oss-security&m=144094021709472
https://infoswift.wordpress.com/2015/08/31/knowledge-tree-xss/
http://japanbroad.blogspot.jp/2015/08/knowledge-tree-bug-exploit.html
http://marc.info/?l=full-disclosure&m=144099659719456&w=4
http://tetraph.blog.163.com/blog/static/234603051201573144123156/
http://www.openwall.com/lists/oss-security/2015/08/30/2
https://www.mail-archive.com/fulldisclosure%40seclists.org/msg02446.html
http://itinfotech.tumblr.com/post/128016383831/knowledge-tree-xss
http://germancast.blogspot.com/2015/08/knowledge-tree-xss.html
http://permalink.gmane.org/gmane.comp.security.oss.general/17655
http://webtech.lofter.com/post/1cd3e0d3_806e1d4